First look at the Azure SQL Managed Instance MP
The Azure SQL Managed Instance is one of Microsoft’s Platform-as-a-Service (PaaS) offerings for SQL. It adds all the features you would expect of a PaaS platform such as automated patching, backups and streamlined high availability whilst closely aligning the technology to on-premises or IaaS workloads to reduce the barrier to entry. The product features near 100% compatibility with the latest Enterprise Edition of SQL Server and the automated Azure Data Migration service. As a result, the product is an attractive option for those looking to lift and shift their existing enterprise applications and commercial-off-the-shelf (COTS) products into the new PaaS world.
Naturally, many of these organizations are going to be using SCOM to monitor their estates and workloads using traditional on-premises or Infrastructure-as-a-Service (IaaS) workflows. Some components of these applications may not currently suit a PaaS architecture and need to retain their current form once the SQL workflows have moved. Therefore they will stay squarely within SCOMs remit.
The managed instance management pack aims to close the gap that the traditional SQL management packs would have filled before the migration to PaaS. The management pack utilizes T-SQL queries to monitor the DB Engine, Databases, Agents, Jobs, Memory-Optimised Data, and Failover Groups allowing a wide variety of monitoring scenarios to be covered. Crucially it will allow for the whole application to continue to be monitored in its totality.
Setting up the MP
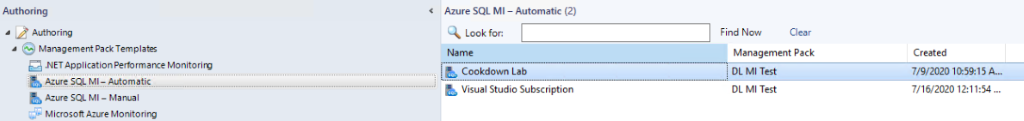
Like the previous version of the management pack one of the ways of monitoring your instances is to manually provide a public or private connection string and the credentials to use it. These are very easy to obtain via the connection strings menu of the Managed Instance itself in the Azure portal. If you don’t have a Gateway or VPN to the network you can use a public connection string, however, this needs to be enabled in the MI Virtual network menu and may require some network security group configuration. My lab environment is entirely situated within Azure so I was able to limit this down to purely Azure resources on setup and then down to only my resources soon after that. For my lab environment this is fine, your organisational requirements may preclude this. In general this is a pretty straightforward no-frills discovery tool and isn’t very dynamic. Which brings me on to my personal big ticket feature of the latest version of the Azure Managed Instance Management Pack. It can provide automatic discovery by leveraging Enterprise Applications and the Azure Active Directory Graph API to discover and monitor your instances. No manual connections required!
https://www.cookdown.com/blog/first-look-at-the-azure-sql-managed-instance-mp